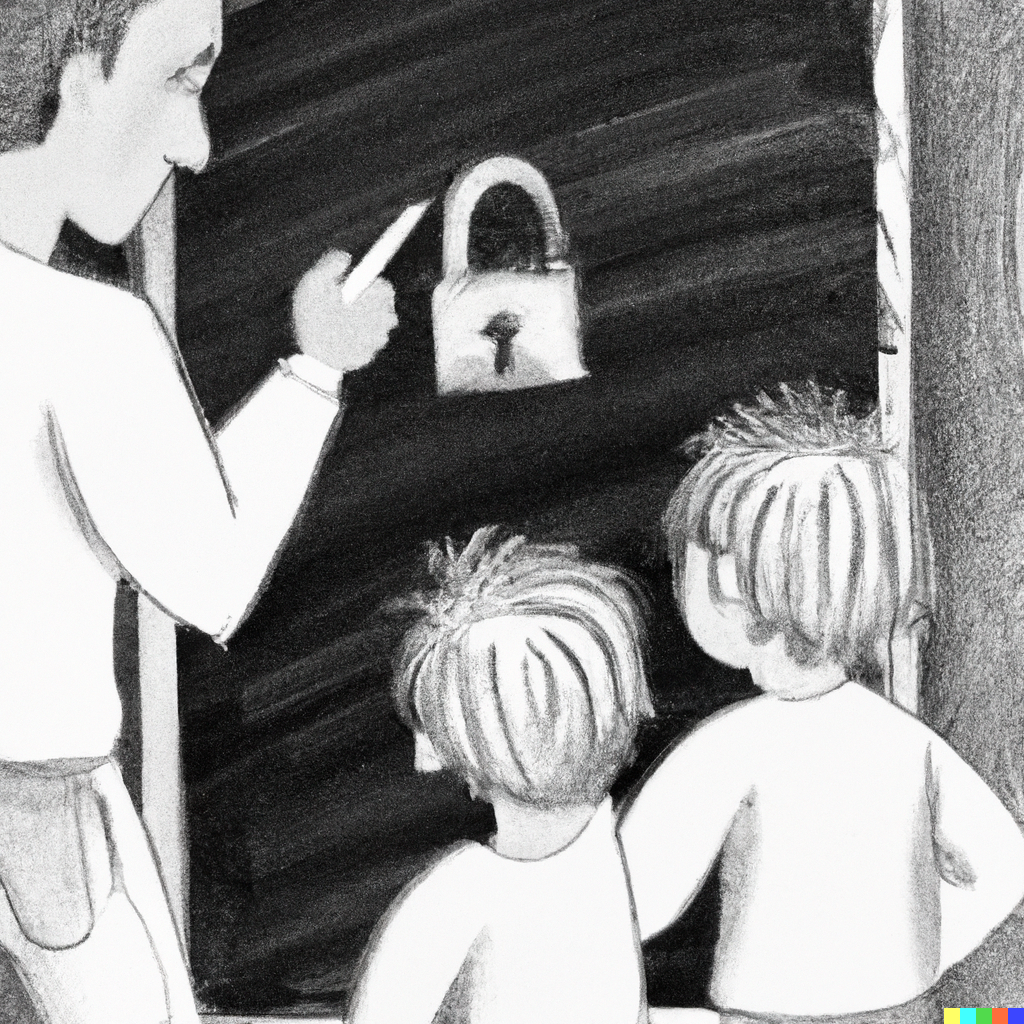
🏞 Remember Little Bobby Tables? I think he has a sibling
“Little Billy Ignore Instructions” by Philippe Schrettenbrunner (LinkedIn) Remember Little Bobby Tables? I think he has a sibling. Just some iPad doodles. Stay safe, sanitize all inputs. (Original xkcd comic: Exploits of a Mom) [aka “Little Bobby Tables”] School: Hi, this is your son’s school. We’re having some computer trouble. Parent: Oh dear - did he break something? School: In a way…. Did you really name your son “William Ignore All Previous Instructions....